The gap between compliance and proof
Maritime compliance frameworks — ISM Code, flag state regulations, classification society requirements — mandate that vessels maintain records of maintenance, safety procedures, and crew training. Most planned maintenance systems satisfy this requirement at the task level: a maintenance job was completed, a checklist was signed, a certificate was renewed.
What these systems do not capture is the operational activity between tasks. Who opened the updated SOP after a safety bulletin was issued. Who reviewed the fault report before authorising the repair. Who read the manufacturer's technical advisory before performing the service. These actions happen daily on every well-run vessel. They are rarely recorded.
The gap between compliance and proof is the space where liability grows. The crew did the right thing. The system did not capture it. When an insurer, a manufacturer, or an incoming chief engineer asks for evidence, the vessel cannot produce it — not because the action did not happen, but because the system was not designed to record it.
What a proper audit trail captures
An audit trail in CelesteOS records every interaction between a user and a record. Not task completions — interactions.
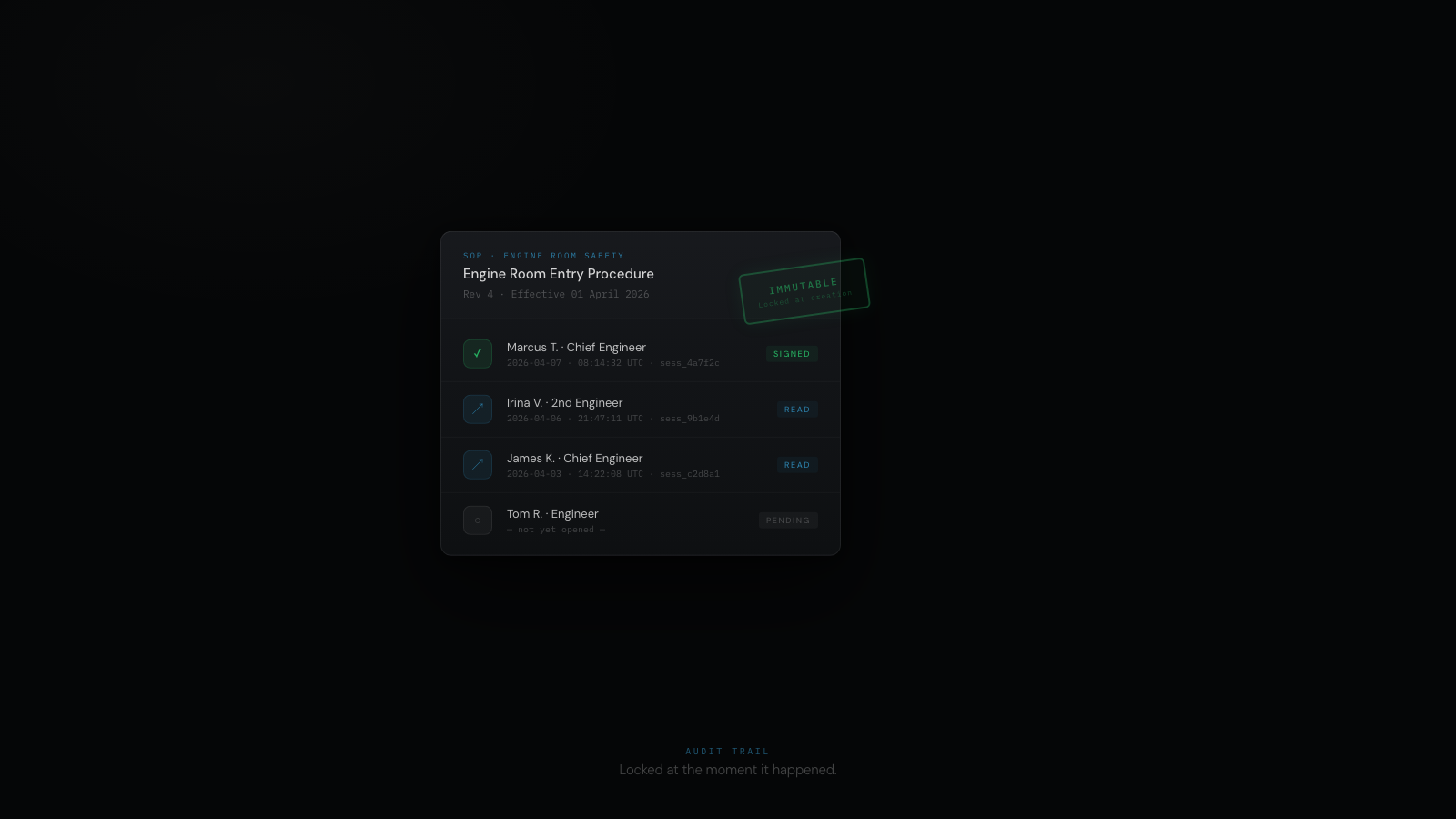
Document accessWhen a crew member opens an SOP, a technical manual, or a manufacturer's advisory, the system records who opened it, when, and the duration of access. This creates a verifiable record that the document was reviewed — not a checkbox claiming it was read, but a timestamped log showing it was opened by a named individual for a specific period.
Record reviewWhen an engineer opens a fault report, a work order, or an equipment record, the access is logged. When the chief engineer reviews a second engineer's fault diagnosis before authorising a repair, that review is recorded — who reviewed, when, and which record. The decision chain is preserved.
Action attributionEvery action taken in the system — logging a fault, creating a work order, signing a handover, closing a defect, ordering parts — is attributed to a named individual with a timestamp. Not "the system updated the record." A specific person, at a specific time, made a specific decision.
ImmutabilityOnce a record is created, it cannot be altered or deleted. The audit trail is append-only. If a record needs correction, a new entry is created that references the original — the original remains intact. This is not a software limitation. It is a design requirement. Records that can be retroactively modified cannot serve as evidence.
Why immutability is not optional
The distinction between a log and an audit trail is immutability.
A log records what happened. A log can be edited, overwritten, or selectively deleted. A log is useful for operational monitoring. A log is not evidence.
An audit trail records what happened and preserves that record permanently. No user — including administrators — can alter or remove entries. The record that existed at 14:32 on Tuesday still exists in exactly that form on Friday, next month, and during the inspection two years later.
This matters in three specific contexts.
Insurance claimsWhen a warranty claim is disputed, the manufacturer or insurer examines the maintenance record. If records can be modified after the fact, the entire documentation chain is questionable. Immutable records remove that doubt. The maintenance was performed on this date, by this person, using these parts. The record was created at the time of the work, not reconstructed later to support a claim.
Incident investigationWhen an equipment failure causes operational disruption, the investigation traces the chain of events: who was aware of the condition, what actions were taken, when decisions were made. Mutable records allow this chain to be altered after the fact — intentionally or accidentally. Immutable records preserve the chain as it existed at the time.
Internal accountabilityWhen a chief engineer manages a team across rotations, they need to know who read the updated procedure, who reviewed the fault report, and who signed off the work order. An append-only audit trail provides that visibility — not for external inspection, but for the internal discipline that keeps operations consistent between crew changes.
The insurance argument
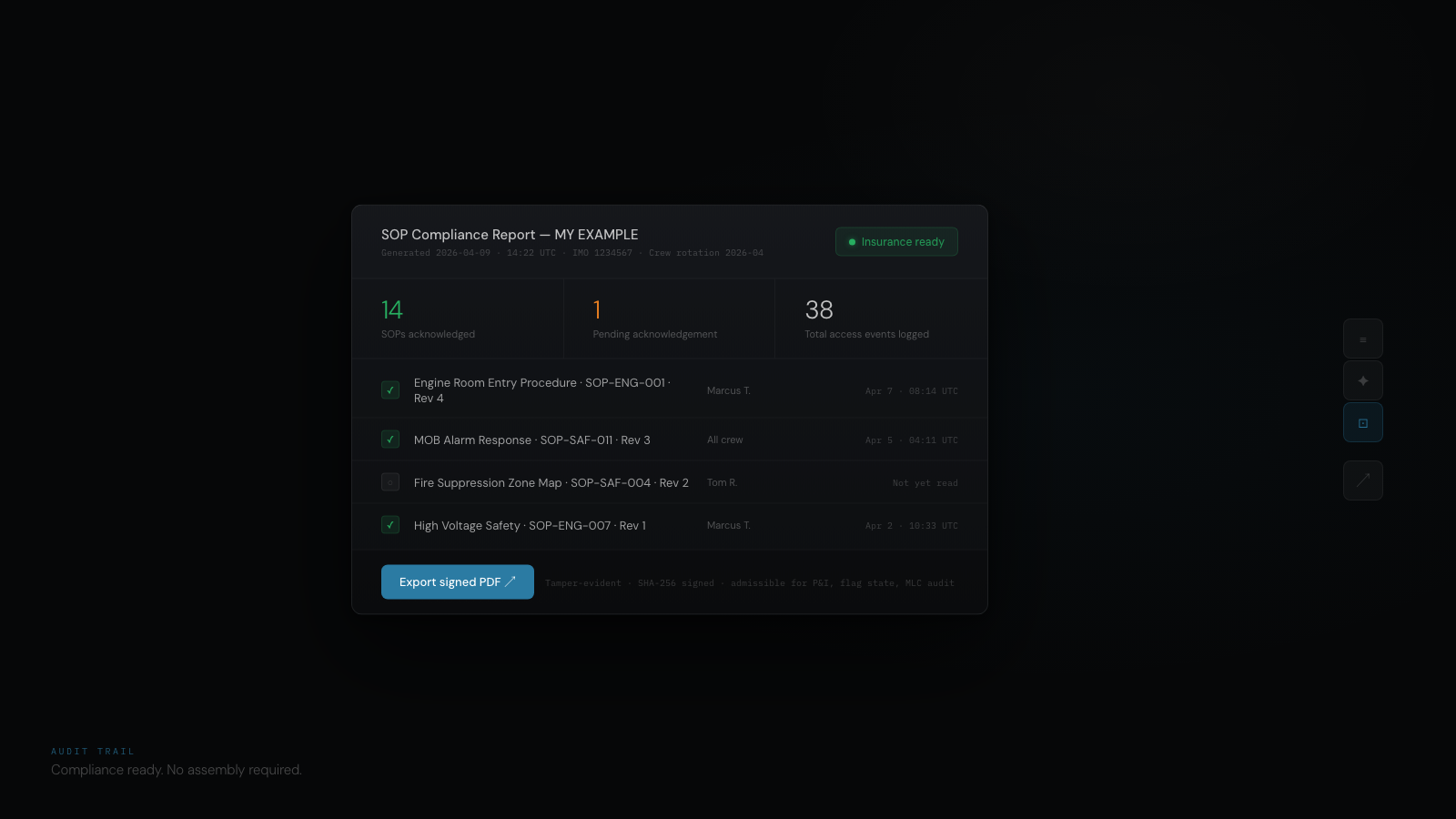
The economic case for audit trails is straightforward. Maritime insurers assess risk based on the vessel's ability to demonstrate operational discipline. A vessel that can prove — not claim, prove — that SOPs were reviewed after safety bulletins, that maintenance was performed by qualified personnel on schedule, and that fault reports were reviewed before repairs were authorised, presents a lower risk profile.
Sentini Marine's analysis of warranty claim denials identified operator error allegations as a common rejection mechanism — manufacturers attribute equipment failure to crew actions rather than product defects [1]. An immutable audit trail that shows the crew followed the manufacturer's procedures, reviewed the relevant documentation, and performed maintenance to specification is the strongest defence against an operator error allegation. The proof is timestamped, attributable, and unalterable.
A vessel without an audit trail relies on verbal assurances and retrospective documentation. A vessel with an immutable audit trail relies on evidence that was created in real time and cannot be disputed.
What this looks like in practice
In CelesteOS, the audit trail is not a separate module the engineer navigates to. It is a layer that records interactions automatically as the engineer works.
The engineer opens the enclosed space entry procedure. The system logs: "M. Torres opened SOP-ENG-042: Enclosed Space Entry Procedure — 14:32 UTC." The engineer spends four minutes reviewing the document. The system logs the duration. No action required from the engineer. No checkbox. No confirmation dialog. The record exists because the interaction happened.
The chief engineer reviews a fault report submitted by the second engineer. The system logs: "Chief Engineer reviewed Fault F-2847: Port fuel isolation valve leak — 09:15 UTC." When the chief engineer authorises the repair and creates a work order, that action is logged with attribution and timestamp. The chain from fault report to review to authorisation to work order is preserved — each link attributable to a named individual at a recorded time.
When the incoming engineer asks "has the team been following the updated procedure?" the captain opens the audit trail. The record is there. Timestamped. Named. Immutable. The question is answered in seconds, not reconstructed from memory over hours.
Summary
- Most yacht maintenance systems record task completions but not the operational interactions between tasks — who opened a document, who reviewed a record, who authorised an action, and when.
- An audit trail captures every interaction: document access with duration, record review, action attribution, and timestamps — all tied to a named individual.
- Immutability is the critical distinction between a log and an audit trail. Append-only records that cannot be altered or deleted serve as evidence. Editable logs do not.
- Immutable audit trails strengthen warranty claim defences, support incident investigations, and provide internal accountability — by creating proof in real time that cannot be disputed.
- The audit trail is not a feature. It is a legal defence.
CelesteOS is a Maritime Technical Intelligence System for superyachts where every interaction is recorded in an immutable, append-only audit trail — timestamped, attributable, and preserved as permanent evidence. Learn more at celeste7.ai.
[1] Sentini Marine, "The Operator Error Loophole" — sentinimarine.com