When the inspector asks
A port state inspector steps aboard during a routine visit. The vessel is well maintained. The crew is experienced. The documentation is in order — certificates current, maintenance logs up to date, safety equipment serviced. Then the inspector asks a question that most vessels cannot answer.
"Following the enclosed space incident reported in February — can you confirm that all crew reviewed the updated entry procedure?"
The captain knows they did. The chief engineer briefed the team on a Tuesday morning. Every crew member read the revised SOP. But knowing is not proving. The inspector does not need the captain's assurance. The inspector needs a record: who opened the document, when, and whether they read it in full.
On most vessels, that record does not exist. The procedure was reviewed. The proof was never captured.
Having records is not the same as having evidence
Maritime compliance frameworks require vessels to maintain records of maintenance, safety procedures, and crew training. Most planned maintenance systems satisfy this at the task level — a job was completed, a checklist was signed, a certificate was renewed.
What these systems do not capture is the activity between tasks. Who opened the updated SOP after a safety bulletin was issued. Who reviewed the fault report before authorising the repair. Who read the manufacturer's technical advisory before performing the service.
The gap between compliance and proof is the space where liability grows. When an insurer disputes a warranty claim, when a manufacturer alleges operator error, when a flag state surveyor issues a non-conformity — the vessel's defence depends on records that most systems were never built to create.
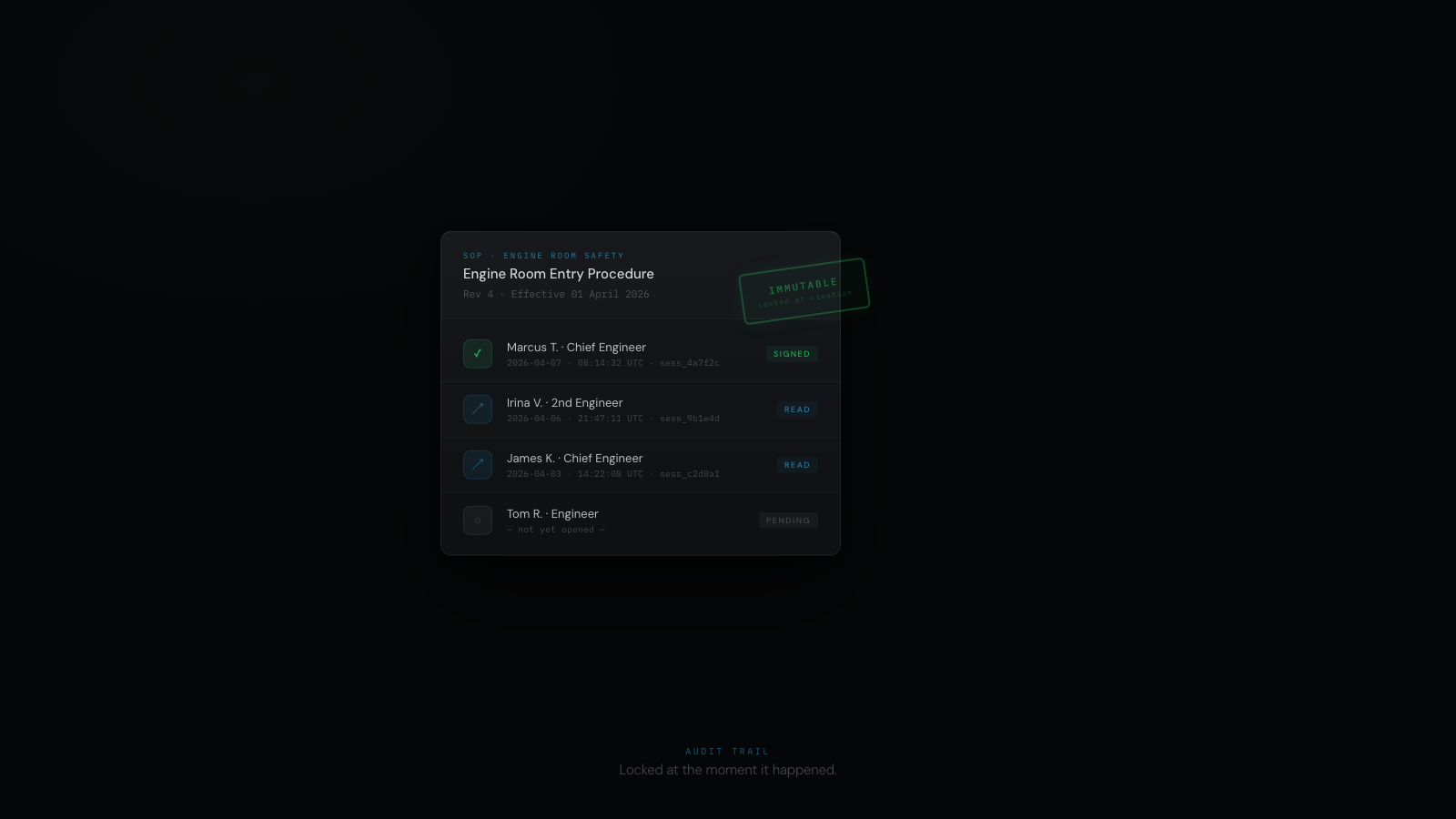
Every action has a name and a timestamp
An audit trail records every interaction between a crew member and a record. Not task completions — interactions.
Document access. When a crew member opens an SOP, a technical manual, or a manufacturer's advisory, the system records who opened it, when, and for how long. Not a checkbox claiming the document was read — a timestamped log showing it was opened by a named individual for a measured duration.
Record review. When an engineer opens a fault report or a work order, the access is logged. When the chief engineer reviews a second engineer's fault diagnosis before authorising a repair, that review is recorded — who reviewed, when, which record.
Action attribution. Every action — logging a fault, creating a work order, signing a handover, closing a defect, approving a purchase order — is attributed to a named individual with a timestamp. A specific person, at a specific time, made a specific decision.
Immutability. Once created, a record cannot be altered or deleted. The audit trail is append-only. If a correction is needed, a new entry is created that references the original — the original remains intact. Records that can be retroactively modified cannot serve as evidence. Immutability is not a feature. It is a legal requirement for defensible documentation.
When the question is asked — and it will be — the answer is in the system
The economic case for immutable audit trails is measured in claims that are defended rather than denied.
Warranty claims. When a manufacturer disputes a claim and alleges operator error, the vessel needs to prove that maintenance was performed to specification, by qualified personnel, using approved parts, within the required service interval. An immutable audit trail shows the exact sequence: who performed the work, when, what parts were used, and that the relevant SOP was reviewed before the procedure. The proof is timestamped, attributable, and unalterable.
Incident investigation. When an equipment failure causes operational disruption, the investigation traces the chain of decisions: who was aware of the condition, what actions were taken, when. Mutable records allow this chain to be altered after the fact. Immutable records preserve it as it existed at the time.
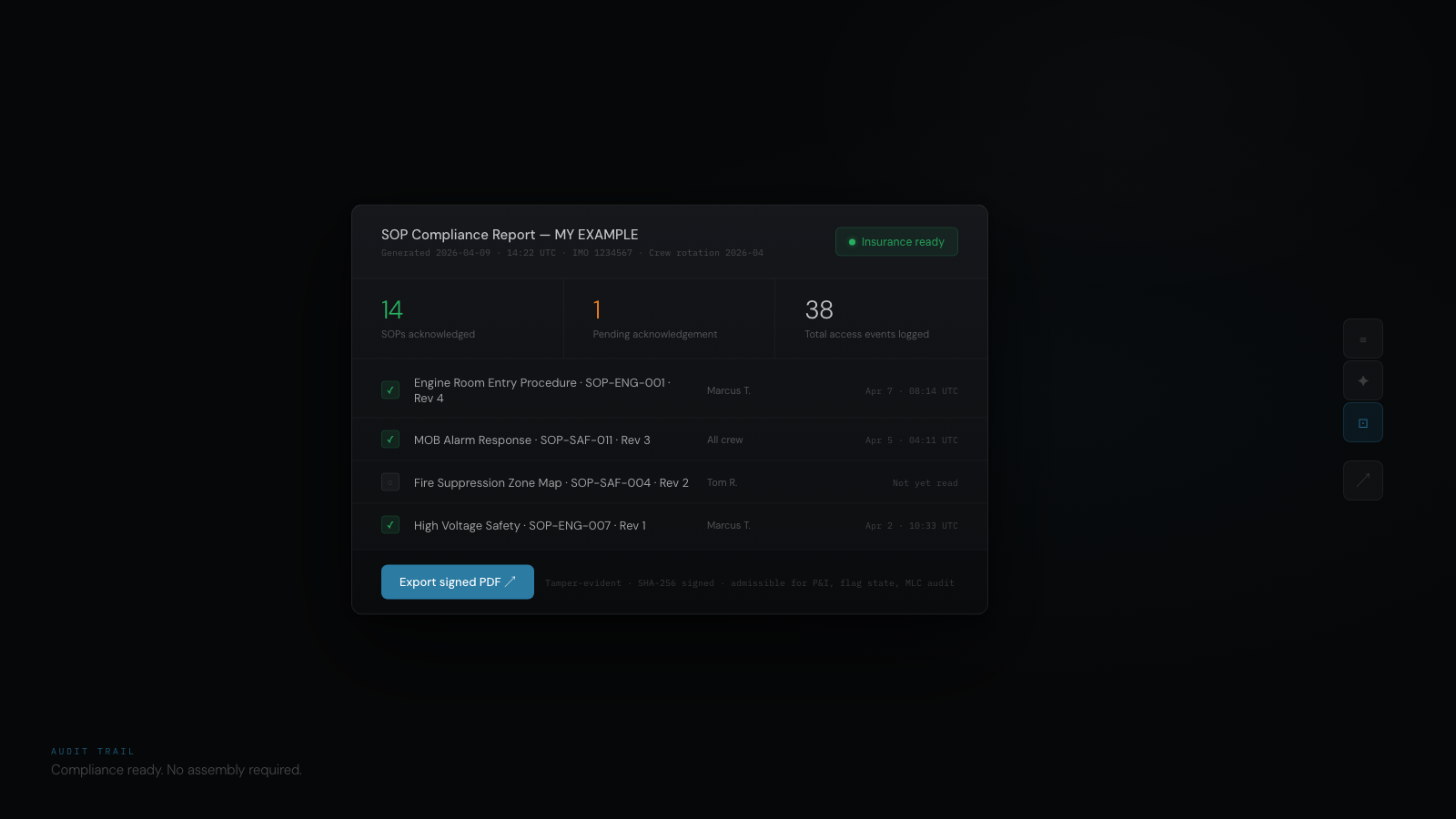
Insurance risk profile. A vessel that can demonstrate — through verifiable records, not verbal assurances — that SOPs are reviewed, maintenance is performed on schedule, and every action is attributable, presents a measurably lower risk profile. Inspection readiness is not preparation. It is what has already been recorded.
How the audit trail works
CelesteOS is a Maritime Technical Intelligence System for superyachts. The audit trail is not a separate module the engineer navigates to. It is a layer that records interactions automatically as the crew works.
An engineer opens the enclosed space entry procedure. The system logs the access — who, when, duration. No action required from the engineer. No checkbox. No confirmation dialog. The record exists because the interaction happened.
When the chief engineer reviews a fault report and authorises a repair, the decision chain is preserved automatically: fault reported, reviewed by chief engineer, work order created, parts authorised, work completed, signed off. Each link attributable to a named individual at a recorded time.
The question is answered in seconds.
The audit trail is not a feature. It is a legal defence.
When an inspector asks, the answer exists. When an insurer questions, the evidence is timestamped. When a manufacturer alleges operator error, the proof is immutable.
Operational discipline deserves operational proof. The gap between what a vessel's crew actually does and what a vessel can prove it did is where liability grows — and where defensible records close the gap.
Structured pilot programme
If you manage vessels and defensible records matter to your operation, we should talk.
contact@celeste7.ai →